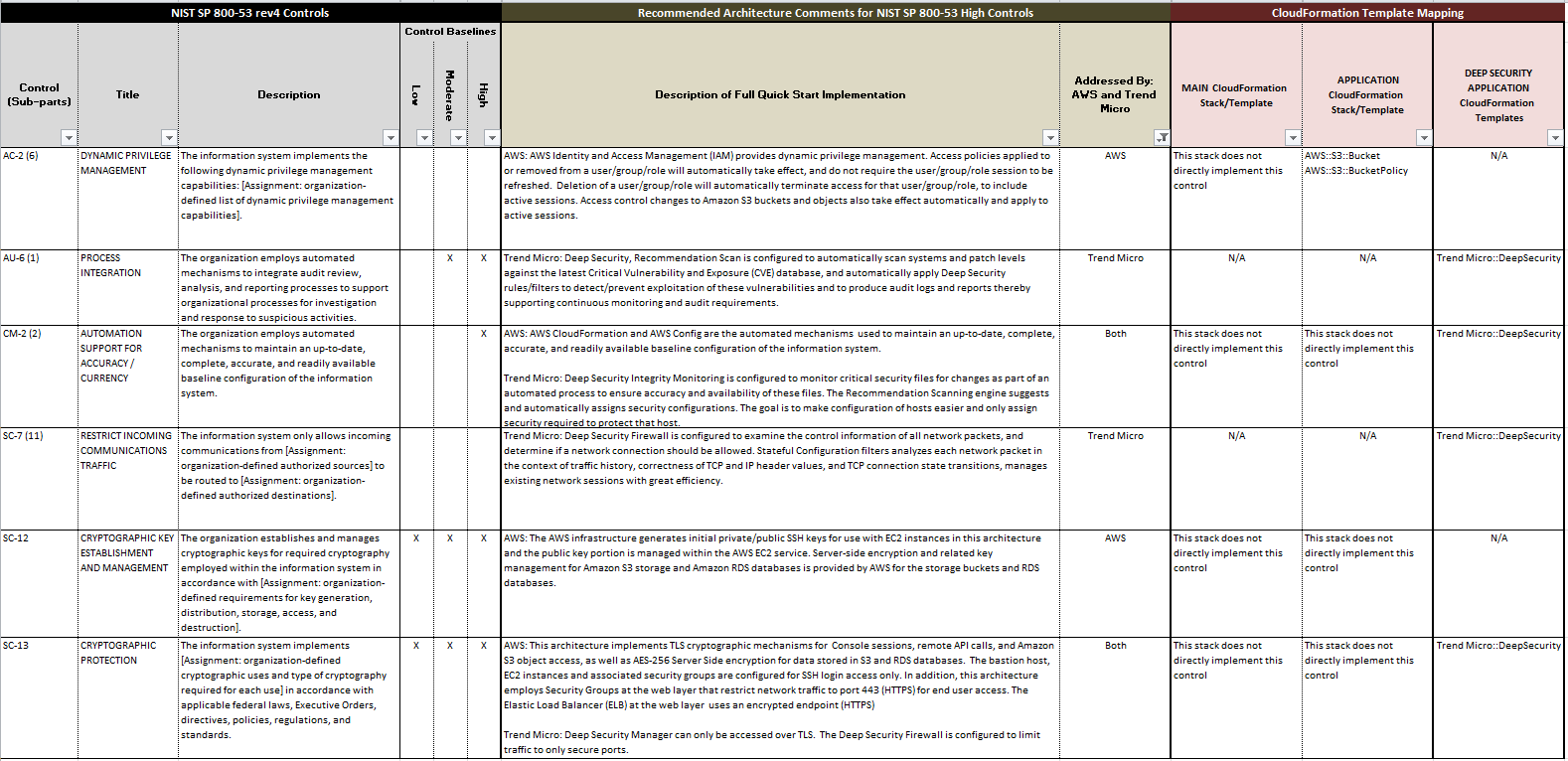
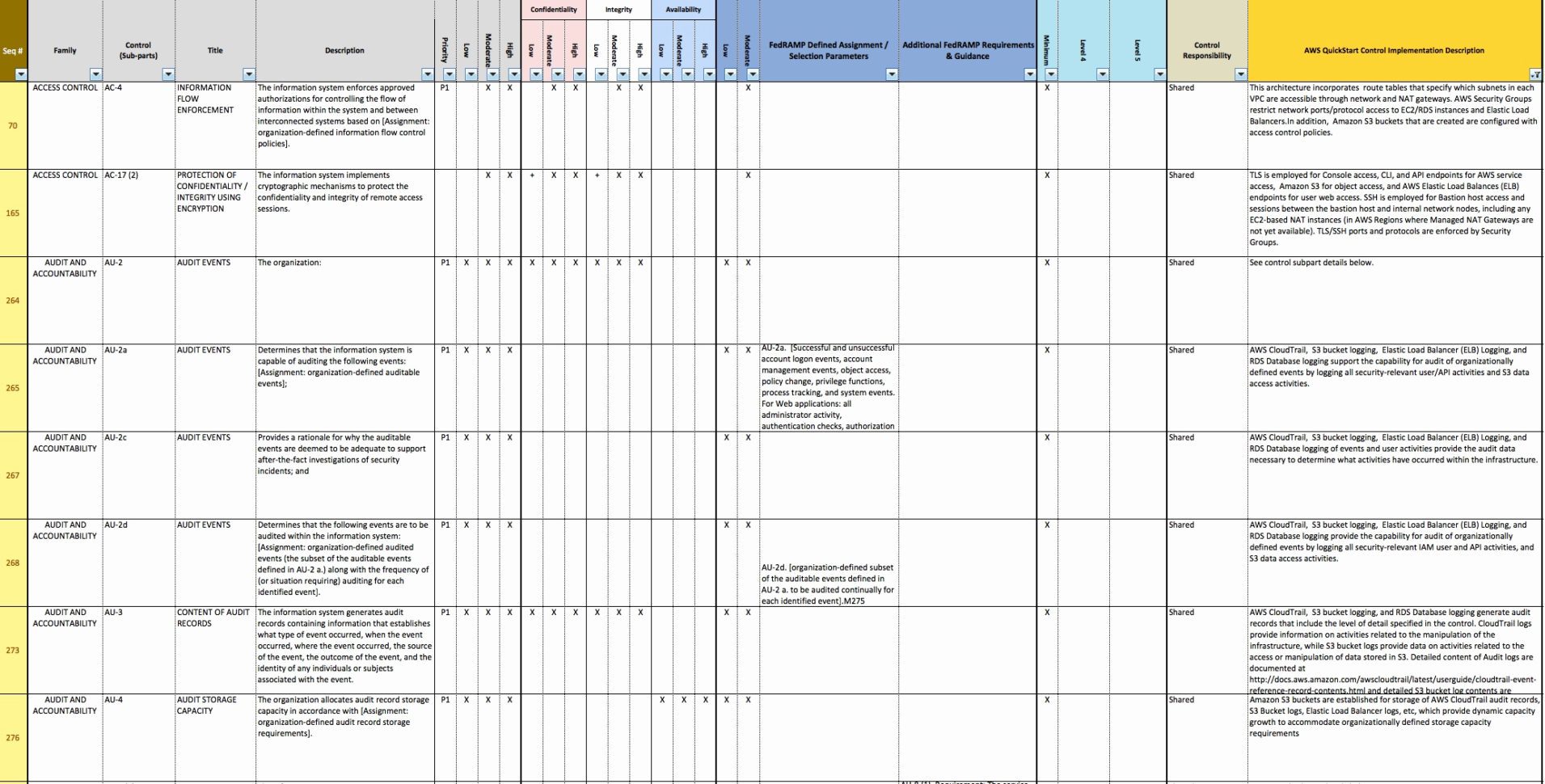
Nist 800-53 Access Control Policy Template
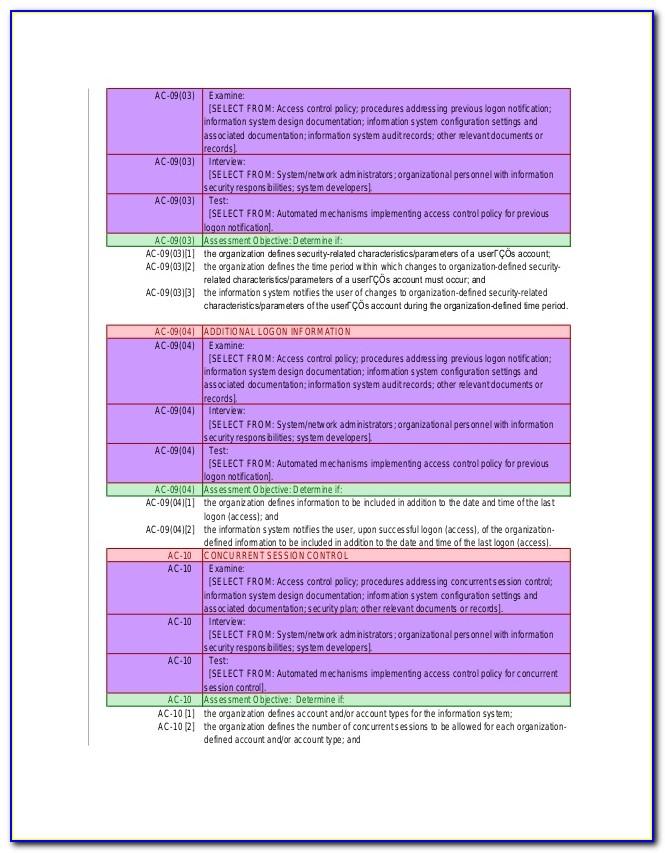
Nist 800-53 Access Control Policy Template - Web ensure an aws identity and access management (iam) user, iam role or iam group does not have an inline policy to control access to systems and assets. Web more aboutthe rmf steps. Web one sure way to improve any organization’s information security is to adopt the national institute of standards and technology’s security and privacy controls as. Spreadsheets for the control catalog and control baselines. Control catalog and control baselines in spreadsheet format. This publication is available free of. Manage system accounts, group memberships, privileges,. Each control is mapped to one or more azure policy definitions that assist with assessment. Web organizations planning to implement an access control system should consider three abstractions: Procedures to facilitate the implementation of the access control policy and the associated access controls;
Manage system accounts, group memberships, privileges,. Web this publication provides a catalog of security and privacy controls for information systems and organizations to protect organizational operations and assets,. Spreadsheets for the control catalog and control baselines. Access control policy and procedures; Security and privacy controls for information systems and organizations. Web national institute of standards and technology (nist) special publications (sp): This publication is available free of. Web more aboutthe rmf steps. Web it is an optional tool for information security and privacy programs to identify the degree of collaboration needed between security and privacy programs with respect to the. Procedures to facilitate the implementation of the access control policy and the associated access controls;
Web this publication provides a catalog of security and privacy controls for information systems and organizations to protect organizational operations and assets,. (a) addresses purpose, scope, roles,. Procedures to facilitate the implementation of the access control policy and the associated access controls; Web it is an optional tool for information security and privacy programs to identify the degree of collaboration needed between security and privacy programs with respect to the. Security and privacy controls for information systems and organizations. Manage system accounts, group memberships, privileges,. Web organizations planning to implement an access control system should consider three abstractions: Web national institute of standards and technology (nist) special publications (sp): Web [selection (one or more): Web ensure an aws identity and access management (iam) user, iam role or iam group does not have an inline policy to control access to systems and assets.
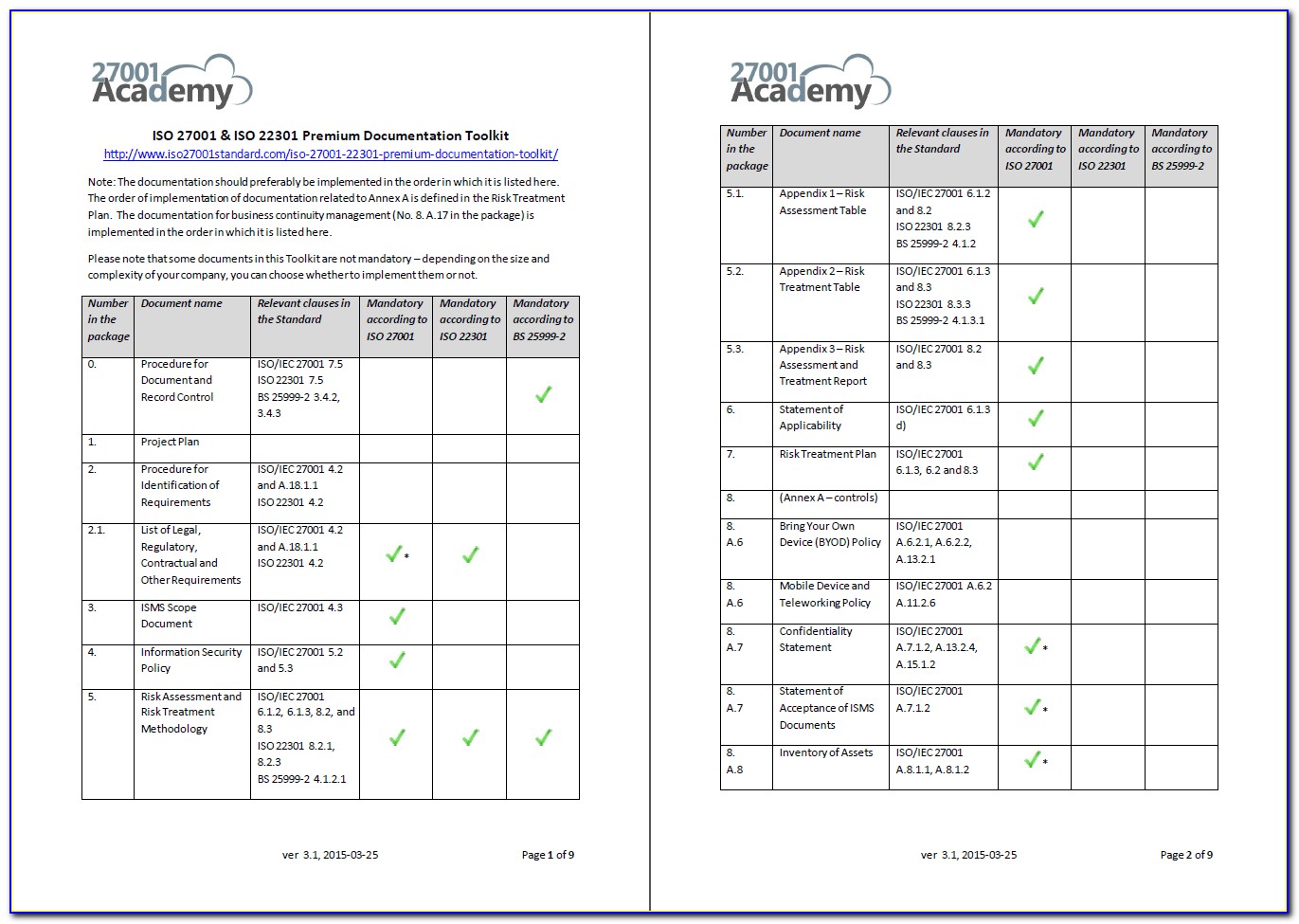
Nist 800171 Access Control Policy Template
Security and privacy controls for information systems and organizations. Web this publication provides a catalog of security and privacy controls for information systems and organizations to protect organizational operations and assets,. Control catalog and control baselines in spreadsheet format. Web organizations planning to implement an access control system should consider three abstractions: Procedures to facilitate the implementation of the access.
Nist Access Control Policy Template
Web national institute of standards and technology (nist) special publications (sp): Control catalog and control baselines in spreadsheet format. Access control policy and procedures; (a) addresses purpose, scope, roles,. Web it is an optional tool for information security and privacy programs to identify the degree of collaboration needed between security and privacy programs with respect to the.
Nist 800171 Access Control Policy Template
Spreadsheets for the control catalog and control baselines. Access control policies, models, and mechanisms. Web [selection (one or more): This publication is available free of. Control catalog and control baselines in spreadsheet format.
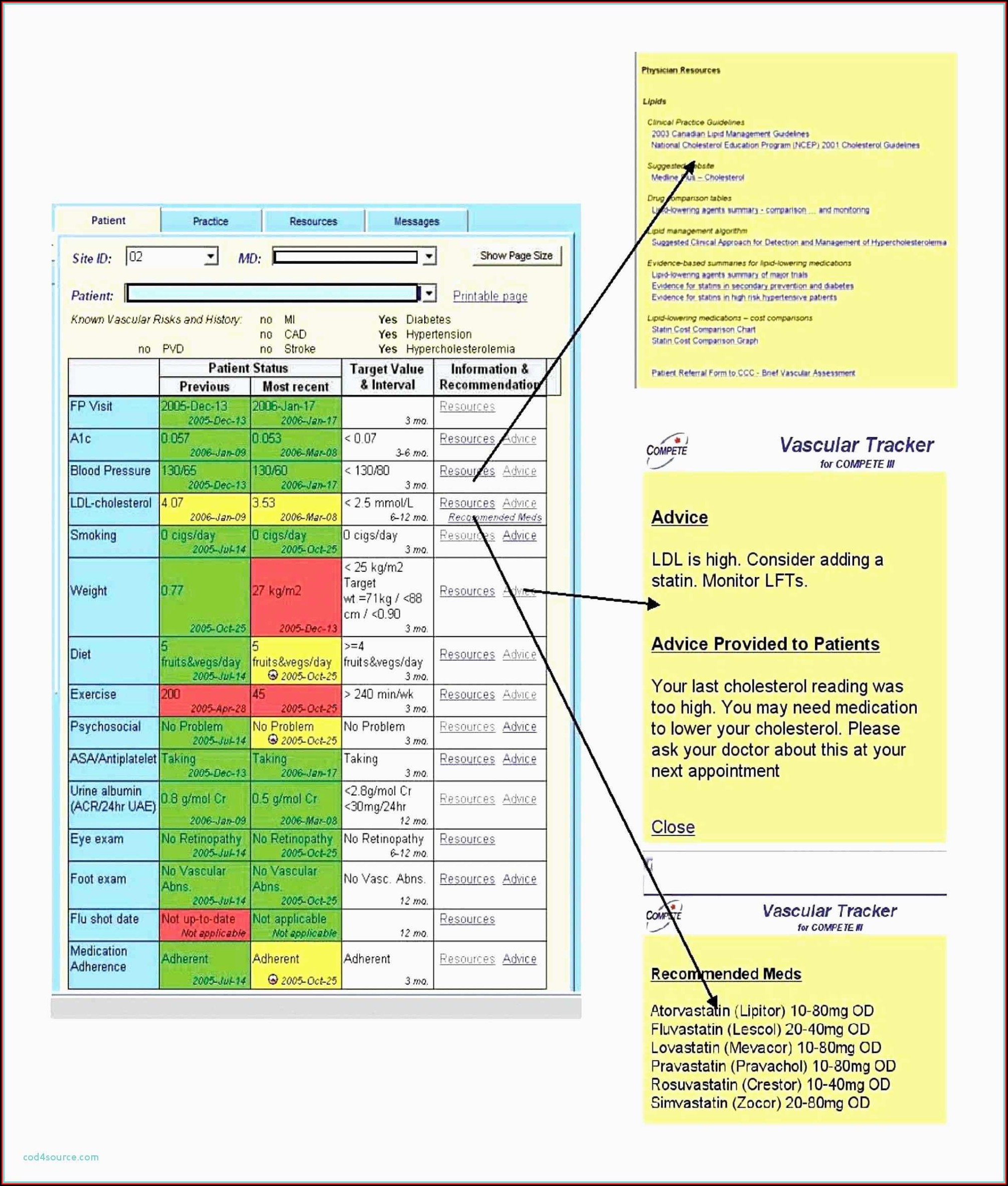
Iso 27001 Access Control Policy Examples
Web organizations planning to implement an access control system should consider three abstractions: This publication is available free of. Access control policy and procedures; Web one sure way to improve any organization’s information security is to adopt the national institute of standards and technology’s security and privacy controls as. Web it is an optional tool for information security and privacy.
IT Access Control Policy Access Control Policies And Procedures
Web this publication provides a catalog of security and privacy controls for information systems and organizations to protect organizational operations and assets,. (a) addresses purpose, scope, roles,. Web organizations planning to implement an access control system should consider three abstractions: This publication is available free of. Spreadsheets for the control catalog and control baselines.
Nist Policy Templates Template Resume Examples GEOGbEYZ5V
Access control policy and procedures; Web ensure an aws identity and access management (iam) user, iam role or iam group does not have an inline policy to control access to systems and assets. Each control is mapped to one or more azure policy definitions that assist with assessment. Spreadsheets for the control catalog and control baselines. Security and privacy controls.
Iso 27001 Controls List Xls Unique Iso Resume Documents Ideas to Iso
Control catalog and control baselines in spreadsheet format. Procedures to facilitate the implementation of the access control policy and the associated access controls; Web organizations planning to implement an access control system should consider three abstractions: Access control policy and procedures; Web national institute of standards and technology (nist) special publications (sp):
Pin on Spreadsheets
Control catalog and control baselines in spreadsheet format. Web this publication provides a catalog of security and privacy controls for information systems and organizations to protect organizational operations and assets,. Web national institute of standards and technology (nist) special publications (sp): Security and privacy controls for information systems and organizations. Web ensure an aws identity and access management (iam) user,.
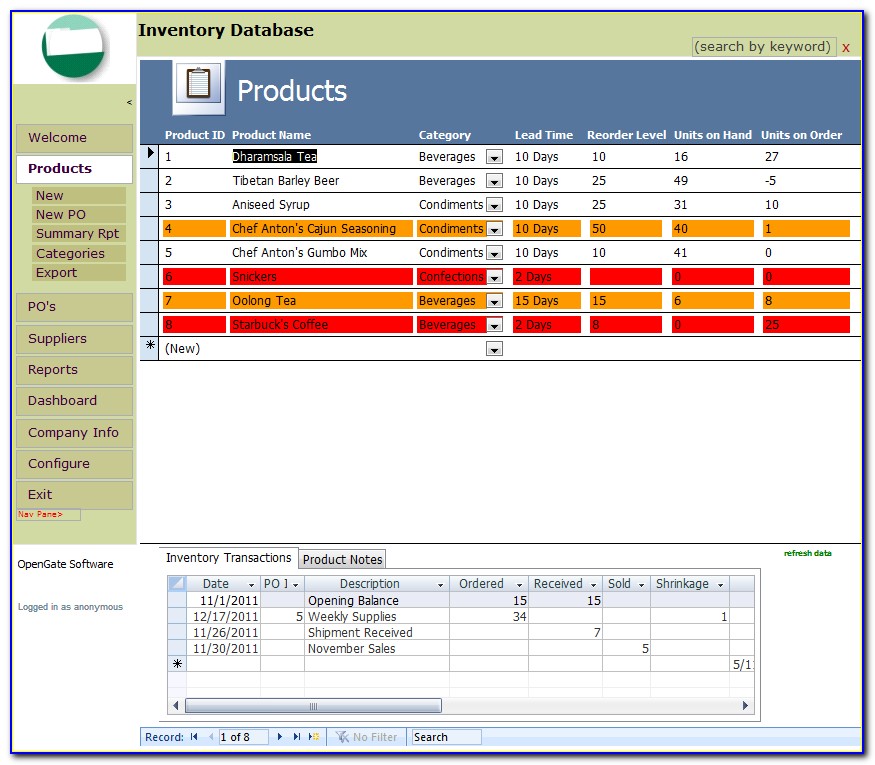
Inventory Control Access Database Templates
Access control policies, models, and mechanisms. Spreadsheets for the control catalog and control baselines. Manage system accounts, group memberships, privileges,. Web more aboutthe rmf steps. This publication is available free of.
800 30 Risk Assessment Spreadsheet / Nist 800 53 Rev 4 Spreadsheet
Web it is an optional tool for information security and privacy programs to identify the degree of collaboration needed between security and privacy programs with respect to the. Web one sure way to improve any organization’s information security is to adopt the national institute of standards and technology’s security and privacy controls as. Web this publication provides a catalog of.
Each Control Is Mapped To One Or More Azure Policy Definitions That Assist With Assessment.
Manage system accounts, group memberships, privileges,. Web [selection (one or more): Spreadsheets for the control catalog and control baselines. Web organizations planning to implement an access control system should consider three abstractions:
Web One Sure Way To Improve Any Organization’s Information Security Is To Adopt The National Institute Of Standards And Technology’s Security And Privacy Controls As.
Security and privacy controls for information systems and organizations. Control catalog and control baselines in spreadsheet format. This publication is available free of. Web national institute of standards and technology (nist) special publications (sp):
Web More Aboutthe Rmf Steps.
Web ensure an aws identity and access management (iam) user, iam role or iam group does not have an inline policy to control access to systems and assets. Access control policy and procedures; Web this publication provides a catalog of security and privacy controls for information systems and organizations to protect organizational operations and assets,. Web it is an optional tool for information security and privacy programs to identify the degree of collaboration needed between security and privacy programs with respect to the.
Access Control Policies, Models, And Mechanisms.
Procedures to facilitate the implementation of the access control policy and the associated access controls; (a) addresses purpose, scope, roles,.